Every business and property owner wants to keep their assets safe, but when it comes to handing out keys, things can spiral fast. A single lost or duplicated key can put an entire organization at risk. Yet, studies reveal that effective key control policies can reduce unauthorized access risks by over 70 percent. Most people focus on who holds the keys, but the real security starts with how those keys are managed in the first place.
Table of Contents
- What Are Key Control Policies And Their Importance?
- Why Key Control Policies Matter For Security
- How Key Control Policies Function In Real-World Scenarios
- Key Concepts Behind Effective Key Control Strategies
- Practical Applications Of Key Control Policies For Various Property Types
Quick Summary
| Takeaway | Explanation |
|---|---|
| Implement key control policies for security | Establishing structured protocols significantly reduces risks of unauthorized access and enhances accountability. |
| Customize strategies for different environments | Tailor key control approaches to fit unique security needs of residential, commercial, or institutional settings. |
| Focus on tracking and accountability | Implement detailed tracking mechanisms and authorization protocols to ensure proper key management and reduce vulnerabilities. |
| Recognize legal and financial implications | Poor key management can lead to legal issues, litigation, and financial losses for organizations. |
| Adopt advanced technological solutions | Use electronic systems and biometric authentication for more efficient and secure key management practices. |
What are Key Control Policies and Their Importance?
Key control policies represent strategic protocols designed to manage, track, and secure physical and digital access through key management systems. These comprehensive guidelines establish precise rules about who can access specific keys, when they can be used, and under what circumstances.
Understanding the Core Principles
At their fundamental level, key control policies serve as comprehensive security frameworks that protect organizational and personal assets. These strategic systems define clear procedures for key distribution, tracking, and accountability across various environments like residential properties, commercial spaces, and institutional settings.
Key control policies typically encompass several critical components:
- Detailed key inventory management
- Strict authorization protocols
- Comprehensive tracking mechanisms
- Clear procedures for key replacement and recovery
Significance in Security Management
The importance of robust key control policies cannot be overstated. By implementing structured key management protocols, organizations and property owners can significantly reduce unauthorized access risks.
Effective key control minimizes potential security breaches and creates transparent accountability for key holders.
Businesses and property managers recognize that uncontrolled key circulation represents a substantial security vulnerability. A single unreturned or duplicated key can compromise entire security systems, potentially exposing sensitive areas to unauthorized entry.
For those seeking more comprehensive insights, read more about master key systems that offer advanced key control strategies for complex organizational environments.
Ultimately, key control policies transform keys from simple metal objects into sophisticated access management tools. They provide a structured approach to security that balances accessibility with stringent protective measures, ensuring that the right people have the right access at the right time.
This table summarizes the fundamental components and principles of effective key control policies as highlighted throughout the article, offering a clear overview for quick reference.
| Principle/Component | Description |
|---|---|
| Key Inventory Management | Maintaining detailed records of all keys issued and in use |
| Authorization Protocols | Strict rules on who may access, issue, or return keys |
| Tracking Mechanisms | Monitoring movement and usage of each key |
| Key Replacement Procedures | Steps for prompt action if a key is lost, stolen, or damaged |
| Regular Audits | Periodic checks to ensure compliance and identify gaps |
| Technological Integration | Use of electronic logs, biometrics, or smart key systems |
| Accountability Policies | Clear assignment of responsibility for all key holders |
Why Key Control Policies Matter for Security
Key control policies represent more than just administrative procedures they are critical safeguards protecting organizations, properties, and individuals from potential security vulnerabilities. Understanding their strategic importance illuminates how systematic key management prevents unauthorized access and potential breaches.
Risk Mitigation Through Structured Protocols
According to workplace security research, uncontrolled key distribution creates significant organizational risks. Comprehensive key control policies serve as proactive defense mechanisms that systematically reduce potential security threats by establishing clear accountability and tracking mechanisms.
Key risks that effective key control policies address include:
- Unauthorized personnel accessing sensitive areas
- Potential theft or property damage
- Compromised internal security infrastructure
- Reduced ability to track key movements
Financial and Legal Implications
Beyond physical security, key control policies carry substantial financial and legal implications. Organizations without robust key management strategies expose themselves to potential litigation, insurance complications, and significant financial losses. A single compromised key can result in extensive damages that far exceed the cost of implementing comprehensive key control systems.
Learn more about advanced security strategies that complement traditional key control approaches and provide multi layered protection for complex environments.
Businesses and property managers must recognize that key control is not an optional security feature but a fundamental requirement. By implementing systematic tracking, authorization protocols, and clear replacement procedures, organizations transform potential security vulnerabilities into managed, controllable access points.
Ultimately, effective key control policies represent an investment in comprehensive security infrastructure an approach that prioritizes prevention over reactive measures and provides peace of mind for property owners and managers.
How Key Control Policies Function in Real-world Scenarios
Key control policies transform theoretical security concepts into practical, actionable strategies that protect physical and digital assets across diverse organizational environments. These sophisticated systems go beyond simple lock and key management, creating comprehensive frameworks for access control and accountability.
Implementation in Organizational Settings
Research from security management experts demonstrates that effective key control policies require multilayered approaches tailored to specific organizational needs. Real-world implementation involves creating intricate systems of authorization, tracking, and restricted access.
Typical key control policy implementation includes:
- Detailed key issuance documentation
- Strict authentication protocols
- Regular key auditing procedures
- Clear guidelines for key return and replacement
Practical Application Across Different Environments
Different sectors require unique key control strategies. A hospital might implement different protocols compared to a manufacturing facility or educational institution. Each environment demands customized approaches that balance security with operational efficiency.
Explore advanced master key systems that provide flexible access management solutions for complex organizational structures.
For instance, in corporate settings, key control policies might involve electronic tracking systems, biometric authentication, and hierarchical access levels. Property management companies might use sophisticated key management software that logs every key movement, creating transparent accountability.
The most effective key control policies are dynamic systems that adapt to changing security landscapes. They incorporate technological innovations, understand human behavior, and create robust mechanisms that prevent unauthorized access while maintaining operational flexibility.
Ultimately, successful key control policies are not about restricting movement but about creating intelligent, responsive security ecosystems that protect assets, people, and organizational integrity.
Key Concepts Behind Effective Key Control Strategies
Key control strategies represent sophisticated security frameworks that extend far beyond traditional lock and key management. These intricate systems combine technological innovation, human behavior understanding, and strategic planning to create comprehensive access management solutions.
Fundamental Principles of Key Management
Research from security management professionals reveals that effective key control strategies rely on several core principles. Successful implementations integrate multiple layers of protection and accountability to minimize potential security vulnerabilities.
Critical foundational concepts include:
- Comprehensive key tracking mechanisms
- Hierarchical access authorization
- Regular security audits and assessments
- Technological integration and adaptability
Strategic Approach to Access Control
Effective key control goes beyond physical key distribution. Modern strategies incorporate digital tracking, biometric authentication, and intelligent access management systems that provide real time monitoring and instant accountability.
Learn more about key duplication prevention and understand the critical importance of controlling key reproduction in comprehensive security frameworks.
Organizations must develop nuanced approaches that consider unique operational requirements. A manufacturing facility might require different key control strategies compared to a healthcare institution or educational campus. The goal remains consistent create secure, flexible systems that protect assets while maintaining operational efficiency.
Technological advancements have transformed key control from a reactive security measure to a proactive, intelligent management system. Electronic key cabinets, blockchain verified access logs, and artificial intelligence driven monitoring represent the cutting edge of modern key control strategies.
Ultimately, successful key control is about creating adaptive, intelligent systems that understand and respond to complex security landscapes while maintaining human centered design principles.
Practical Applications of Key Control Policies for Various Property Types
Key control policies are not one-size-fits-all solutions but sophisticated systems tailored to specific property requirements. Different environments demand unique approaches to access management, security protocols, and key tracking mechanisms that address their distinctive operational challenges.
Residential Property Key Control
According to property security research, residential key control involves creating comprehensive systems that protect homeowners while maintaining convenient access. Effective residential key policies focus on limiting unauthorized entry and tracking key distribution among family members and authorized personnel.
Key considerations for residential properties include:

- Limited key circulation among trusted individuals
- Clear protocols for key lending and returns
- Secure storage of spare keys
- Immediate key replacement procedures
Commercial and Institutional Key Management
Commercial environments require more complex key control strategies that balance security with operational efficiency. Advanced key management systems integrate technological solutions like electronic access logs, biometric authentication, and hierarchical clearance levels.
Explore advanced master key systems that provide flexible access management for complex organizational structures.
For instance, a hospital might implement strict key control policies that differentiate access levels between departments. Surgical wings might have more restrictive key protocols compared to administrative areas, ensuring patient safety and maintaining confidential information security.
Multi-tenant commercial properties present unique challenges, requiring sophisticated key management that allows individual tenant security while providing property managers with necessary access capabilities. Smart key systems with programmable electronic locks offer dynamic solutions that adapt to changing occupancy and security requirements.
Below is a comparison table that outlines key differences in key control policy application and focus between residential properties and commercial/institutional environments, as described in the article.
| Environment Type | Primary Focus | Key Control Approach | Key Management Features |
|---|---|---|---|
| Residential Property | Limiting unauthorized entry | Limited key circulation among trusted | Secure spare key storage, fast replacement |
| Commercial/Institutional | Balancing security & operations | Hierarchical, tech-enabled key management | Electronic logs, biometrics, audits |
| Multi-tenant Commercial | Tenant security vs. manager access | Programmable electronic systems | Dynamic access, adaptable to change |
| Healthcare (Hospital) | Protecting sensitive areas | Department-based differentiated protocols | Restrictive for critical zones |
Ultimately, successful key control policies are adaptive frameworks that understand the nuanced security needs of different property types, creating intelligent systems that protect assets while maintaining operational flexibility.
Take Control of Your Property’s Security in the GTA
After learning about the risks of unauthorized key access and the necessity of solid key control policies, you may wonder how to actually upgrade your safety at home or for your business. Weak key management can lead to anxiety, costly losses, and a constant feeling that your property is exposed. This is why understanding core principles such as strict authorization and thorough key tracking is essential, but having the practical tools and expert support to implement these strategies is even more important.
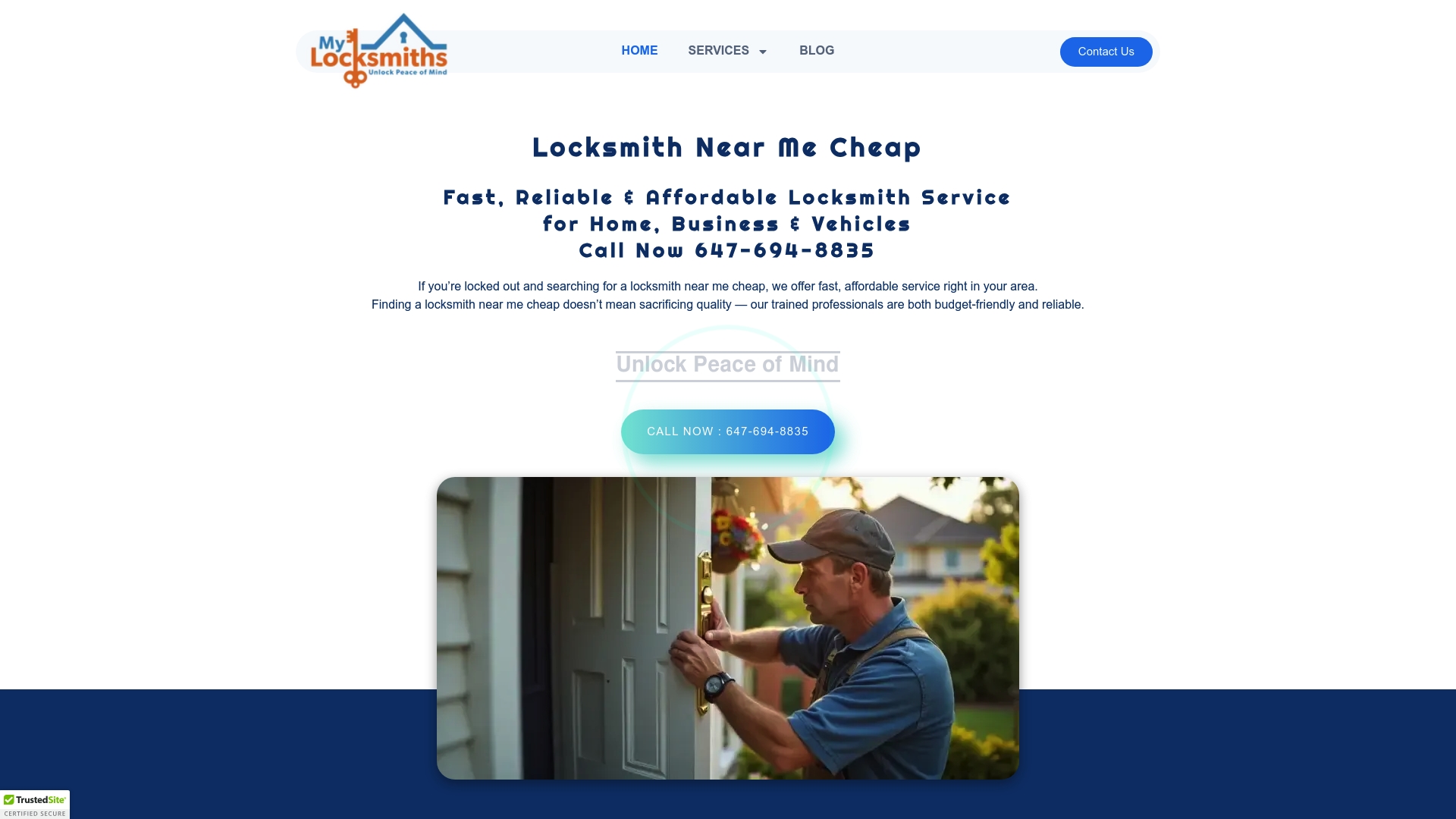
Secure your peace of mind with help from trusted local professionals. At My Locksmiths, we specialize in fast and reliable locksmith solutions across Greater Toronto. If you need rekeying, high-security lock upgrades, or custom access control, our licensed technicians handle everything using the latest techniques discussed in this article. Do not leave your security vulnerable. Visit our homepage now or reach out to schedule a no-obligation consultation and take the first step toward a safer, more controlled environment today.
Frequently Asked Questions
What are key control policies?
Key control policies are strategic protocols designed to manage, track, and secure access through key management systems. They define rules regarding who can access specific keys, when keys can be used, and the procedures for key distribution and accountability.
Why are key control policies important for my home or business?
Key control policies are crucial as they minimize unauthorized access risks, protect assets, and ensure transparency for key holders. They help prevent potential security breaches and can reduce financial and legal liabilities related to compromised keys.
How can I implement key control policies in my business?
To implement key control policies, create a structured system that includes detailed key issuance documentation, strict authorization protocols, regular key audits, and clear guidelines for key return and replacement tailored to your organizational needs.
What factors should I consider for residential key control?
For residential key control, focus on limiting key circulation among trusted individuals, establishing protocols for key lending and returns, securely storing spare keys, and having immediate key replacement procedures in place.







