Keys do a lot more than just fit into a lock. There are over 20 billion keys in worldwide circulation right now, each controlling access to something valuable. Most people think they are just simple pieces of metal, easy to copy with the right tools. But here is the twist. The technology and strategies behind key security are getting so advanced that copying even a single key can now involve strict verification, digital coding, and even biometric checks. It is a world of high-stakes protection hidden in plain sight.
Table of Contents
- What Are Keys and Their Function in Security?
- Why Key Duplication Matters for Individuals and Businesses
- The Process of Key Duplication: How It Works
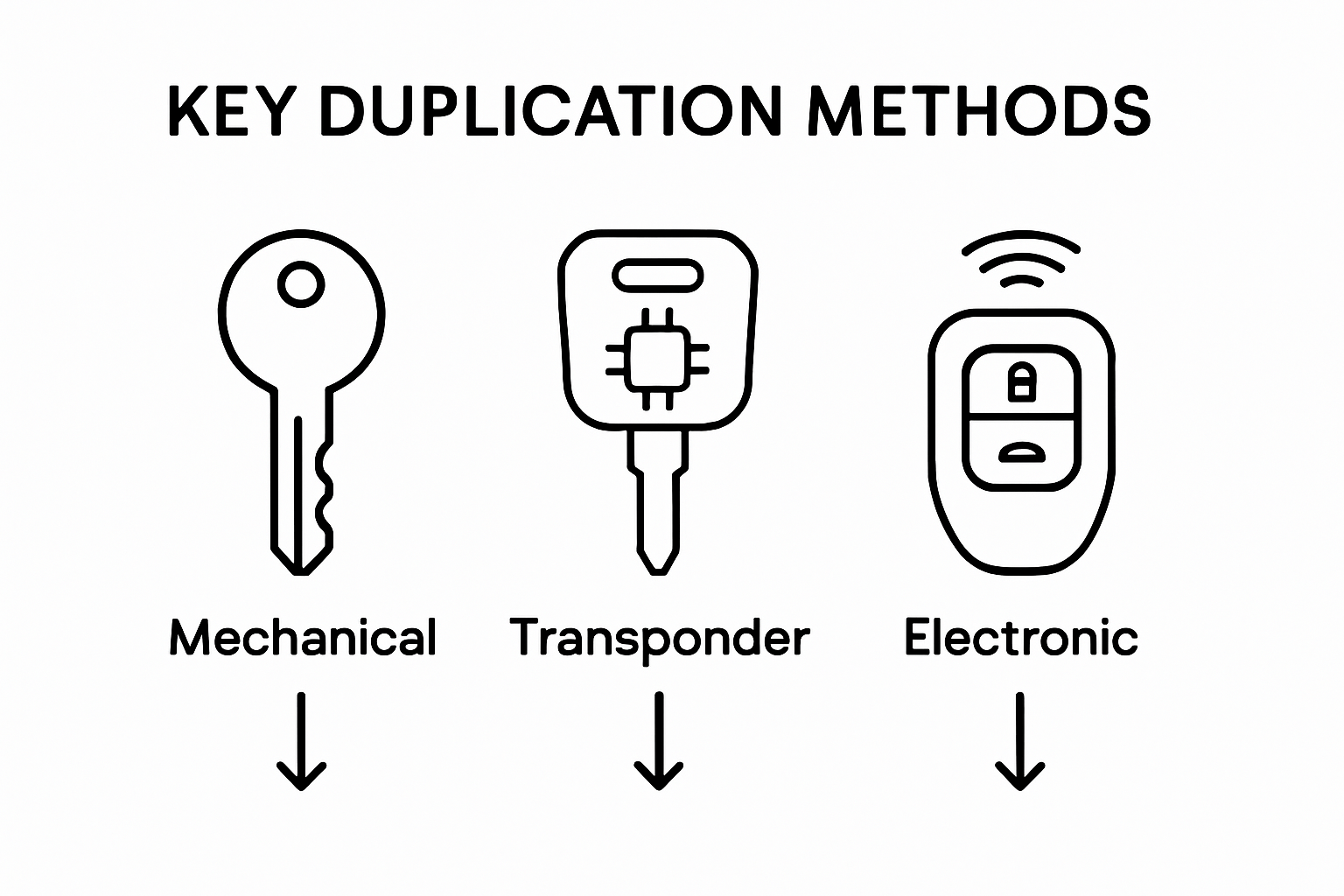
- Different Methods of Key Copying: An Overview
- Key Security: Understanding Risks and Precautions
Quick Summary
| Takeaway | Explanation |
|---|---|
| Keys control access effectively. | Keys serve as essential security tools, allowing authorized entry and blocking unauthorized access in various settings. |
| Key duplication requires strict protocols. | Duplicate keys should be managed carefully to prevent unauthorized access, ensuring a balance between convenience and security. |
| Advanced technologies enhance key security. | Innovations like biometric keys and electronic systems provide better tracking and protection than traditional mechanical keys. |
| Secure key management is critical. | Organizations must implement structured strategies for tracking key distribution and managing access to enhance overall security. |
| Understand key vulnerabilities and risks. | Identifying risks such as unauthorized duplication and lost keys helps to develop effective security measures and protocols. |
What Are Keys and Their Function in Security?
Keys represent sophisticated mechanical or electronic devices designed to control and regulate access to secured spaces, systems, and valuable resources. At their core, keys function as precision security instruments that enable authorized entry while preventing unauthorized access. Understanding their fundamental mechanics reveals how these small objects play a critical role in protecting personal and professional environments.
The Basic Mechanism of Keys
A key operates through a precise interaction between its unique physical profile and the corresponding lock mechanism. Each key contains a specific configuration of cuts, ridges, and grooves that align perfectly with internal lock components. When inserted, these intricate details manipulate internal pin stacks or electronic sensors, creating a precise alignment that permits rotation and unlocking. Key security experts from the National Locksmith Association confirm that this mechanical precision makes keys far more complex than simple metal objects.
Types of Keys and Security Functions
Keys serve multiple security purposes across different domains. In residential settings, they control home entry. In commercial environments, they manage restricted areas. In automotive contexts, they prevent vehicle theft. Keys can be categorized into several primary types:
- Mechanical Keys: Traditional metal keys with physical cut patterns
- Electronic Keys: Smart keys using digital encryption and radio frequency
- Transponder Keys: Advanced automotive keys with embedded microchips
- Biometric Keys: Advanced security keys using personal identification markers
Security Implications and Access Control
Beyond simple entry, keys represent sophisticated access control mechanisms. They create hierarchical security structures, allowing different levels of authorization. A comprehensive security study from MIT indicates that key systems enable organizations to manage complex access requirements, tracking who enters specific spaces and when.
By understanding keys as intricate security instruments, individuals and businesses can better appreciate their role in comprehensive protection strategies.
To clarify the main types of keys and their unique security roles, the table below summarizes their characteristics and primary functions.
| Key Type | Main Characteristics | Primary Security Function |
|---|---|---|
| Mechanical Keys | Metal keys with unique cut patterns | Traditional home, office, and vehicle use |
| Electronic Keys | Use digital encryption and radio frequency | Smart locks and advanced access control |
| Transponder Keys | Embedded with microchips; communicates with receivers | High-security automotive applications |
| Biometric Keys | Use personal identification markers (e.g., fingerprints) | Highest-level security for sensitive areas |
| Whether protecting personal property or managing complex institutional access, keys remain fundamental to modern security infrastructure. |
For more insights into advanced key management, learn about our master key systems.
Why Key Duplication Matters for Individuals and Businesses
Key duplication represents a critical aspect of security management that balances convenience with controlled access. While seemingly straightforward, the process involves complex considerations for protecting personal and professional spaces. Understanding the nuanced implications of key copying helps individuals and organizations maintain robust security protocols.
Strategic Access Management
Key duplication serves multiple strategic purposes beyond simple convenience. For businesses, creating duplicate keys allows for efficient workforce management, enabling multiple employees to access necessary spaces while maintaining accountability. In residential settings, spare keys provide critical backup during emergencies like lockouts or when primary key holders are unavailable. Research from the RCAB Office of Risk Management emphasizes the importance of developing a structured key control policy that manages duplicate key distribution.
Security Risks and Mitigation Strategies
While key duplication offers practical benefits, it simultaneously introduces potential security vulnerabilities. Uncontrolled key copying can lead to unauthorized access, compromising personal and organizational security. Businesses must implement robust key management strategies that include:
- Tracking Key Distribution: Maintaining comprehensive records of who receives duplicated keys
- Limiting Duplication Authorization: Establishing strict protocols for approving key copies
- Regular Security Audits: Periodically reviewing and updating key access permissions
- Using High-Security Key Systems: Implementing keys that are more challenging to duplicate
Technological Evolution in Key Management
Modern key management has transcended traditional mechanical approaches, incorporating advanced technological solutions. Electronic and biometric systems provide more sophisticated access control, reducing risks associated with physical key duplication. These systems offer enhanced tracking, immediate access revocation, and more granular control over entry permissions.
By understanding key duplication as a nuanced security strategy, individuals and businesses can develop more comprehensive protection frameworks. Thoughtful key management balances accessibility with robust security protocols.
Learn more about advanced access control solutions that can transform your security approach.
The Process of Key Duplication: How It Works
Key duplication is a precise technical process that transforms a single key into multiple functional replicas. Understanding this intricate procedure reveals the complex craftsmanship behind creating accurate key reproductions that maintain the original’s precise mechanical specifications.
Key Copying Techniques and Mechanisms
Key duplication involves sophisticated technological approaches that ensure precise replication. Professional locksmiths utilize specialized equipment designed to capture and reproduce the exact physical characteristics of an original key. The primary methods include mechanical key cutting and advanced digital scanning technologies. Each technique requires meticulous precision to guarantee the duplicate key functions identically to the original.
The following table compares key copying techniques, highlighting their main tools and typical applications.
| Copying Technique | Main Tools/Technology Used | Typical Application |
|---|---|---|
| Tracing Method | Manual or automatic duplicator, master key | Residential/standard office keys |
| Impression Method | Blank key, lock, file | When original key is unavailable |
| Code Cutting | Manufacturer-specific numerical code, machine | High-volume, institutional, or automotive |
| Punch Key Method | Punch tools, measurement guides | Restricted keys, precise duplication |
| Laser Scanning | 3D laser scanners, CAD systems | Smart keys, high-security key replication |
| RFID Cloning | Electronic programmers, RFID scanner | Electronic access systems |
The core principles of key duplication center on capturing and reproducing three critical key attributes:
- Key Profile: The precise shape and depth of cuts
- Metal Composition: Using equivalent metal quality and hardness
- Dimensional Accuracy: Matching exact measurements within microscopic tolerances
Professional vs Unauthorized Key Copying
Professional key duplication differs significantly from unauthorized copying. Licensed locksmiths follow strict protocols to verify ownership and authorization before creating key duplicates. Williams College’s Facilities Department guidelines emphasize that key duplication requires proper authentication and should only be performed by authorized professionals.
Authorized key copying involves several critical verification steps:

- Ownership Confirmation: Verifying the individual’s right to duplicate the key
- Original Key Inspection: Examining the key’s condition and authenticity
- Legal and Ethical Compliance: Adhering to institutional and legal requirements
Technological Advancements in Key Replication
Modern key duplication has evolved beyond traditional mechanical methods. Advanced technologies like laser scanning and computerized key cutting machines enable unprecedented levels of precision. These technologies can reproduce complex key designs, including those with intricate security features found in high-security systems.
Learn more about our specialized car key duplication services that leverage cutting-edge replication technologies.
Different Methods of Key Copying: An Overview
Key copying represents a nuanced technical process with multiple methodological approaches, each designed to address specific security and functional requirements. Understanding these diverse techniques provides insight into the sophisticated world of key replication and access management.
Mechanical Key Copying Techniques
Traditional mechanical key copying involves direct physical reproduction of a key’s intricate profile. Professional locksmiths utilize specialized key cutting machines that precisely trace and replicate the original key’s exact configuration. These methods require high-precision equipment capable of matching microscopic ridges, grooves, and depth measurements.
Key mechanical copying techniques include:
- Tracing Method: Using a master key as a direct template for cutting
- Impression Method: Creating a key by carefully mapping internal lock mechanisms
- Code Cutting: Reproducing keys using manufacturer-specific numerical codes
- Punch Key Method: Utilizing specialized punch tools to create key duplicates
Advanced Electronic and Digital Key Replication
Modern key copying has evolved beyond mechanical approaches, incorporating sophisticated digital technologies. Electronic key replication involves complex scanning and programming processes that go far beyond simple physical reproduction. These advanced methods are particularly crucial for sophisticated security systems like automotive and smart lock technologies.
Digital key replication strategies encompass:
- Laser Scanning: Capturing three-dimensional key profiles with exceptional precision
- Computer-Aided Design (CAD) Replication: Using digital modeling for exact key reproduction
- Cryptographic Key Duplication: Reproducing encrypted electronic key signatures
- Radio Frequency Identification (RFID) Cloning: Copying electronic key transmission codes
Security Considerations in Key Copying
While key copying technologies continue advancing, security remains paramount. Professional locksmiths and security experts emphasize the importance of strict authorization protocols. Not all keys can or should be duplicated, particularly those with advanced security features designed to prevent unauthorized replication.
Explore our comprehensive car key duplication services that leverage cutting-edge replication technologies while maintaining the highest security standards.
Key Security: Understanding Risks and Precautions
Key security represents a critical component of comprehensive protection strategies, requiring a multifaceted approach to mitigate potential vulnerabilities. Understanding the intricate risks associated with key management helps individuals and organizations develop robust defense mechanisms against unauthorized access and potential security breaches.
Identifying Potential Key Security Vulnerabilities
Key security risks extend far beyond simple physical loss. Sophisticated threats can emerge through various channels, including unauthorized duplication, social engineering, and technological exploitation. Professional security experts emphasize that every key represents a potential entry point that requires meticulous protection and strategic management.
Critical vulnerabilities in key security systems include:
- Unauthorized Duplication: Risks associated with easily reproducible key designs
- Lost or Stolen Keys: Potential for unauthorized access after key misplacement
- Worn or Damaged Keys: Increased vulnerability due to mechanical degradation
- Insufficient Key Control Protocols: Lack of systematic tracking and management
Strategic Key Protection Mechanisms
The U.S. Department of Justice report highlights the importance of implementing comprehensive key control strategies. Effective protection involves a holistic approach that combines technological solutions, administrative protocols, and continuous monitoring.
Key security enhancement strategies encompass:
- Advanced Key Tracking Systems: Implementing digital inventory management
- Restricted Keyway Designs: Using specialized key profiles difficult to duplicate
- Regular Security Audits: Periodic comprehensive reviews of key distribution
- Access Management Protocols: Establishing clear guidelines for key issuance
Technological Innovations in Key Security
Emerging technologies are revolutionizing key security, providing more sophisticated protection mechanisms. Advanced solutions like biometric authentication, encrypted digital keys, and intelligent access control systems offer unprecedented levels of security beyond traditional mechanical approaches.
These technological innovations enable more granular control, real-time monitoring, and immediate access revocation capabilities. Organizations can now implement dynamic security frameworks that adapt to changing threat landscapes.
Discover how smart lock technologies can enhance your security strategy.
Safeguard Your Security with Trusted Key Duplication and Locksmith Expertise
After reading about the precision and risks involved in key copying, you deserve confidence that your property is truly protected. Whether you are concerned about unauthorized duplication, ensuring the accuracy of spare keys, or need support with advanced lock and access control solutions, the complexity of key management can be overwhelming. The peace of mind that comes from licensed, verified locksmith support is just a step away.
Ready to take control of your key security and eliminate guesswork? Connect with My Locksmiths, your reliable partner for professional key duplication, lock repairs, and emergency lockout services across Toronto. Our technicians understand the advanced techniques and strict security protocols highlighted in this guide, offering you:
- Precise and secure key duplication
- 24/7 emergency response
- Friendly, licensed experts serving Etobicoke, Oakville, Vaughan, and Richmond Hill
Act now and protect what matters most. Schedule your service or learn more about our car key duplication or master key systems to upgrade your security today.
Frequently Asked Questions
How do locksmiths duplicate keys?
Locksmiths duplicate keys by using specialized machines that cut and shape a new key to match the original’s profile. They may employ methods such as tracing, impressioning, or code cutting to ensure precision.
What are the differences between mechanical and electronic key copying?
Mechanical key copying involves physical replication of a key’s design using cutting machines, while electronic key copying includes advanced techniques like laser scanning and programming for smart keys, which often incorporate encryption features for added security.
Are there security risks associated with key duplication?
Yes, risks exist such as unauthorized duplication, lost or stolen keys, and insufficient key control protocols. It’s crucial to have strict authorization processes in place to mitigate these vulnerabilities.
How can I ensure the security of duplicated keys?
To ensure security, maintain records of key distribution, limit duplication authorization to trusted individuals, perform regular audits of key access, and consider advanced key management systems that provide enhanced tracking and control.







