Master key systems sound like something out of a spy movie, but they are real and used in everyday buildings everywhere. Many people think a master key just unlocks every door with no limits, but that is only half the story. The surprise is these systems use a layered design, where a single grand master key can control access to hundreds of locks yet still keep each zone tightly restricted and secure.
Table of Contents
- Defining The Master Key System: What It Is And How It Functions
- Why Master Key Systems Matter: Importance In Security And Access Control
- Key Components And Design: Understanding How A Master Key System Operates
- Real-World Applications: Where Master Key Systems Are Used
- Common Misconceptions: Clarifying The Myths Around Master Key Systems
Quick Summary
| Takeaway | Explanation |
|---|---|
| Master key systems enhance security | They provide precise access management and limit unauthorized entry by carefully mapped key hierarchies. |
| Granular access control improves efficiency | Organizations can streamline access permissions, allowing tailored access for various personnel in different areas. |
| Cost savings with master key systems | A single master key can replace multiple keys, reducing administrative overhead and simplifying key management. |
| Pin tumbler locks enable complex configurations | Specialized internal mechanisms permit multiple keys to operate the same lock without compromising security levels. |
| Common myths about master key systems are misleading | Properly designed systems can offer enhanced security and effective access control, contrary to some prevalent beliefs. |
Defining the Master Key System: What It Is and How It Functions
A master key system represents a sophisticated access control mechanism that enables multiple keys to open a series of locks within a specific hierarchy. Unlike traditional single-key approaches, this system allows different levels of authorized access across various spaces while maintaining centralized control.
The Hierarchical Structure of Master Key Systems
At its core, a master key system operates through a carefully designed hierarchical configuration of keys. According to Towson University’s Key Control Policy, this structure typically includes several key types with progressively broader access rights:
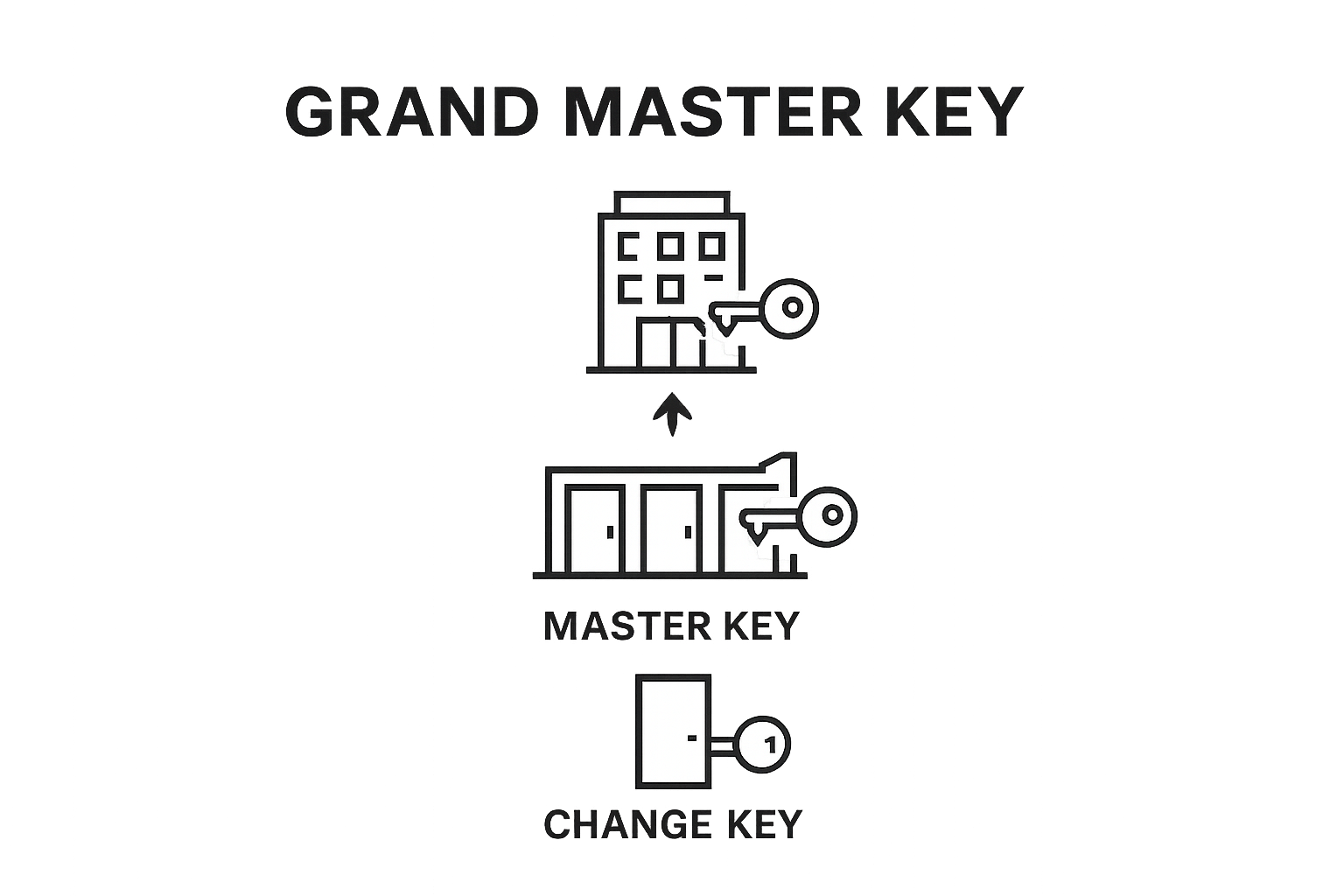
- Change Keys: Lowest level keys providing access to specific individual rooms or areas
- Sub-Master Keys: Opening multiple rooms within a designated section
- Master Keys: Accessing broader sections of a building or facility
- Grand Master Keys: Controlling multiple interconnected areas or buildings
How Master Key Systems Function
The mechanics of a master key system rely on intricate pin tumbler lock designs. Each lock contains multiple pin sets that can be configured to allow different keys to operate simultaneously. This means a building manager can have a grand master key opening every door, while individual department heads might possess master keys for their specific zones, and individual employees receive change keys for their immediate workspaces.
For businesses and organizations, read more about advanced key management strategies, master key systems offer unprecedented flexibility and security. By carefully mapping key hierarchies, administrators can create precise access protocols that balance convenience with stringent security requirements.
The genius of master key systems lies in their ability to provide granular access control without compromising overall security. Each key level is strategically designed to restrict unauthorized entry while enabling authorized personnel seamless movement within their designated areas.
Below is a comparison table outlining the different key types within a master key system and the specific access level each provides.
| Key Type | Access Level Description |
|---|---|
| Change Key | Opens a specific individual room or limited area |
| Sub-Master Key | Opens multiple rooms within a designated section |
| Master Key | Accesses broader sections of a building or facility |
| Grand Master Key | Controls multiple interconnected areas or buildings |
Why Master Key Systems Matter: Importance in Security and Access Control
Master key systems represent far more than a convenient method of managing locks they are strategic security solutions that transform how organizations control physical access. By implementing a carefully designed key hierarchy, businesses and institutions can create robust security frameworks that balance operational efficiency with comprehensive protection.
Enhanced Security and Controlled Access
The primary advantage of master key systems lies in their ability to provide granular access management. According to Cornell University’s Facilities Services, these systems allow administrators to:
- Precisely define who can access specific areas
- Limit unauthorized personnel movement
- Create multilayered security protocols
- Quickly revoke or modify access permissions
For example, a hospital might configure its master key system so that maintenance staff can access general maintenance areas, while restricting their entry into sensitive zones like operating rooms or pharmaceutical storage. Learn more about advanced security strategies that complement traditional master key approaches.
Cost-Effective Security Management
Beyond security, master key systems offer significant economic benefits. Instead of managing multiple complex lock systems, organizations can streamline their security infrastructure. A single master key can replace dozens of individual keys, reducing administrative overhead, minimizing replacement costs, and simplifying key management processes.
Moreover, these systems provide a traceable and accountable method of access control. Each key can be logged, tracked, and monitored, creating a comprehensive audit trail that enhances overall organizational security. The ability to quickly rekey or modify access levels without replacing entire lock systems makes master key systems an intelligent, adaptable security solution for diverse environments.
Key Components and Design: Understanding How a Master Key System Operates
A master key system is an intricate engineering marvel that transforms traditional lock mechanisms into sophisticated access control networks. By employing specialized pin configurations and precise mechanical design, these systems create layered security environments that adapt to complex organizational needs.
Mechanical Engineering of Master Key Locks
At the heart of every master key system are pin tumbler locks with uniquely configured internal mechanisms. According to University of Wisconsin’s Campus Security Guidelines, these locks contain multiple pin sets that can be strategically arranged to accommodate different key types:
- Driver Pins: Standard pins that interact with the key’s cutting
- Key Pins: Unique pins of varying lengths corresponding to specific key profiles
- Master Wafer Pins: Special components enabling multiple key interactions
The genius of this design lies in its ability to allow different keys to operate the same lock simultaneously without compromising individual security levels. Learn more about advanced lock technologies that power these innovative systems.
Precision Key Mapping and Configuration
Master key systems require meticulous planning and precise key mapping. Locksmiths must carefully calculate pin length combinations to ensure each key functions within its designated access hierarchy. This involves creating complex mathematical relationships between different key profiles, allowing a grand master key to open multiple locks while individual change keys remain restricted to specific areas.
The configuration process demands exceptional technical expertise. Locksmiths must consider factors like key complexity, potential security vulnerabilities, and the specific access requirements of the organization. Each lock becomes a carefully crafted puzzle, with pin combinations that provide robust security while maintaining operational flexibility.
Real-World Applications: Where Master Key Systems Are Used
Master key systems transcend theoretical security concepts, finding critical applications across diverse professional environments. These sophisticated access control mechanisms provide organizations with unprecedented flexibility in managing physical security, enabling precise control over who enters specific spaces and when.
Institutional and Commercial Environments
Large organizations rely heavily on master key systems to manage complex access requirements. According to Bowie State University’s Key Management Policy, these systems are particularly valuable in settings that demand granular security management:
- Educational Institutions: Managing access across campuses, laboratories, administrative offices
- Healthcare Facilities: Controlling entry to sensitive medical zones, pharmaceutical storage
- Corporate Headquarters: Securing executive areas, research departments, server rooms
- Government Buildings: Protecting classified spaces, restricting unauthorized personnel movement
Explore advanced commercial security solutions that complement master key system strategies.
Specialized Sector Applications
Beyond traditional institutional settings, master key systems play crucial roles in specialized environments requiring nuanced security protocols. Hospitality industries use these systems to provide housekeeping staff limited access to guest rooms while maintaining overall property security. Similarly, manufacturing facilities implement master key hierarchies to ensure maintenance personnel can perform essential tasks without compromising restricted production areas.
The adaptability of master key systems makes them indispensable across industries.
 By creating intricate yet manageable access frameworks, organizations can simultaneously enhance security, improve operational efficiency, and maintain precise control over their physical spaces.
By creating intricate yet manageable access frameworks, organizations can simultaneously enhance security, improve operational efficiency, and maintain precise control over their physical spaces.
Common Misconceptions: Clarifying the Myths Around Master Key Systems
Master key systems are complex security mechanisms frequently misunderstood by those unfamiliar with their sophisticated design. These intricate access control solutions often become subjects of misconception, leading to potential security strategy errors for organizations and individuals alike.
Security Myths and Misunderstandings
Numerous myths surround master key systems that can compromise understanding of their true capabilities. According to National Shooting Sports Foundation’s Security Guidelines, several prevalent misconceptions need critical examination:
- Myth: Master keys are inherently less secure than individual locks
- Reality: Properly designed systems provide enhanced security control
- Myth: Anyone can duplicate a master key
- Reality: Professional locksmiths implement strict key control protocols
- Myth: Master key systems are prohibitively expensive
- Reality: Long-term cost savings significantly outweigh initial investment
Learn more about key management technologies that address these common misunderstandings.
Practical Security Considerations
Contrary to popular belief, master key systems are not universal access passes. Each key within the hierarchy is meticulously engineered with specific access limitations. Professional locksmiths carefully design these systems to ensure that individual keys provide access only to designated areas, maintaining a precise balance between operational convenience and robust security protocols.
Understanding these nuanced security mechanisms requires dispelling simplistic narratives.
This table summarizes and clarifies some of the most common misconceptions about master key systems alongside the actual facts.
| Misconception | Reality |
|---|---|
| Master keys are less secure than singles | Properly designed systems offer enhanced security control |
| Anyone can duplicate a master key | Strict key control protocols prevent unauthorized duplication |
| Master key systems are too expensive | Long-term savings outweigh initial investment |
Master key systems represent sophisticated engineering solutions that adapt to complex organizational needs, offering flexible yet controlled access management far beyond traditional lock-and-key approaches.
Take Control of Your Security With Trusted Local Experts
Master key systems can seem complex, but confusion and inefficiency should never put your building at risk. If you feel overwhelmed by managing multiple keys or worry about unauthorized access, you are not alone. This article highlights how key control and precise hierarchy make a difference for schools, businesses, and property owners. But understanding is only the first step. You deserve a locksmith partner who can help you put theory into practice.
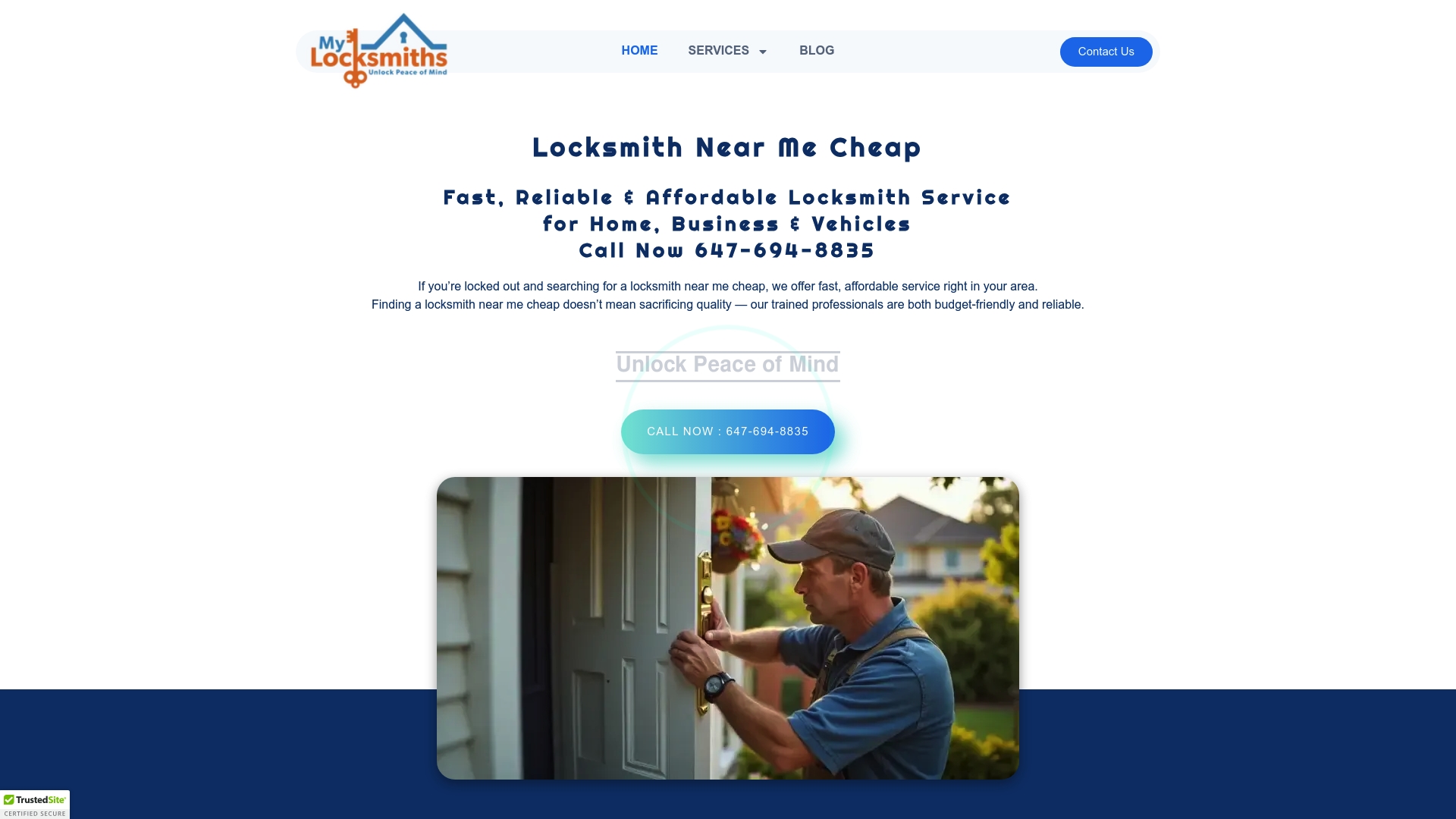
Ready to simplify your access control and make your property safer now? Work with My Locksmiths, your licensed local specialists serving the Greater Toronto Area. Our experienced team is available 24/7 for fast, affordable master key system installations, high-security solutions, rekeying, and more. Do not let vulnerabilities linger. Visit My Locksmiths or request a quote to see why residents and business owners trust us for reliable, professional service. Your security upgrade starts today.
Frequently Asked Questions
What is a master key system?
A master key system is an advanced locking mechanism that allows different keys to open various locks within a set hierarchy, facilitating controlled access across multiple areas while maintaining centralized security management.
How does a master key system work?
Master key systems operate through pin tumbler locks configured to allow multiple keys to function simultaneously. Different keys, including change keys, sub-master keys, and master keys, provide varying levels of access to designated areas.
What are the benefits of using a master key system?
The primary benefits of a master key system include enhanced security through granular access control, cost-effective management by reducing the number of keys required, and simplified tracking of access permissions through audit trails.
Can master key systems be used in different types of organizations?
Yes, master key systems are versatile and can be utilized in institutional settings like schools and hospitals, corporate environments, government buildings, and specialized sectors such as hospitality and manufacturing, allowing tailored access management to meet specific security needs.







