More than 80 percent of commercial buildings rely on some form of master key system for security and access control. Whether managing an apartment complex, a school, or an office, finding the right balance between convenience and security becomes a daily concern. Understanding how master keys work unlocks smarter strategies for protecting property, managing risk, and giving people access where they need it most.
Table of Contents
- Defining A Master Key And Core Purpose
- Types Of Master Key Systems Explained
- How Master Key Systems Function
- Legal And Security Aspects Of Usage
- Benefits, Drawbacks, And Common Pitfalls
Key Takeaways
| Point | Details |
|---|---|
| Master Key Functionality | Master keys provide a hierarchical approach to access control, allowing tailored access for various roles within an organization. |
| Application Versatility | Master key systems are ideal for diverse environments like residential, commercial, and institutional settings, balancing security and convenience. |
| Risk Management Importance | Proper key management protocols are crucial to mitigate security vulnerabilities associated with master keys, especially in case of loss. |
| Benefits and Drawbacks | While offering simplified access management and cost-effective solutions, master key systems also present risks like unauthorized access and complex management requirements. |
Defining a Master Key and Core Purpose
A master key is a specialized key designed with an extraordinary capability: opening multiple locks within a specific system. According to Britannica, it is “a key that can be used to open many locks, such as all the door locks in a building.” This unique key represents a powerful access control mechanism used across residential, commercial, and institutional settings.
At its core, a master key functions through a hierarchical locking system where different keys have varying levels of access. The primary master key can open every lock in the designated set, while subordinate keys might only access specific areas or rooms. This creates a flexible security framework that allows for controlled and strategic access management.
The practical applications of master key systems are extensive. Property managers can grant maintenance staff comprehensive building access while ensuring individual tenants retain privacy for their specific units. Businesses can implement graduated access levels for different employee roles, with senior management holding keys that unlock all areas. Schools, hospitals, and large organizations particularly benefit from these systems, enabling efficient movement and controlled security protocols.
Key characteristics of master key systems include:
- Hierarchical access control
- Centralized key management
- Enhanced security flexibility
- Reduced number of physical keys in circulation
By understanding the fundamental principles of master keys, property owners and managers can design more intelligent and responsive security infrastructures tailored to their specific needs. Learn more about master key systems in our comprehensive guide.
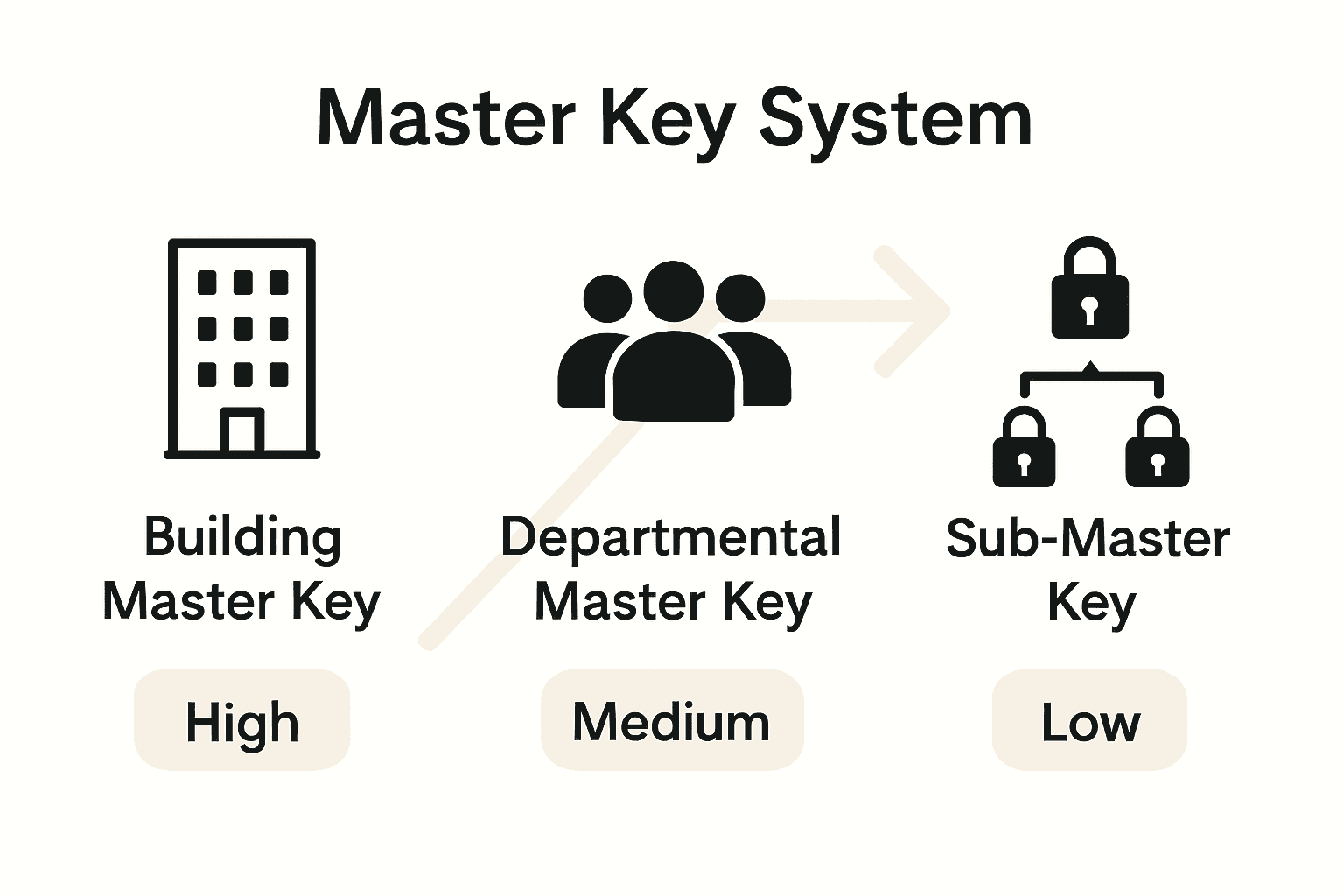
Types of Master Key Systems Explained
Master key systems come in several sophisticated configurations designed to meet diverse security requirements. According to LSA Michigan, a master key system is “a planned locking system in which a group of locks is opened by its own individual keys and also by a special key named Master Key,” providing both security and convenience for users.
The primary types of master key systems include:
- Building Master Key System
- Allows comprehensive access throughout an entire building
- Typically used in commercial and institutional settings
- University of Alaska Fairbanks notes these keys “pose the greatest risk and impact to the key system if lost”
- Departmental Master Key System
- Provides access within specific departments or sections
- Limits key holders to designated areas
- Enhances granular security control
- Sub-Master Key System
- Creates hierarchical access levels
- Allows different management tiers varying levels of entry
- Supports complex organizational security structures
Each system offers unique advantages depending on an organization’s specific security needs. Property managers, facility administrators, and security professionals carefully design these systems to balance accessibility with robust protection.
Selecting the Right System
Choosing an appropriate master key system requires careful assessment of:
- Total number of locks
- Required access levels
- Organizational complexity
- Potential security risks
By understanding these different master key configurations, organizations can implement more intelligent and responsive security infrastructures. Learn more about key control strategies in our comprehensive guide on master key systems.

How Master Key Systems Function
Master key systems operate through a sophisticated hierarchical mechanism that enables strategic access control. According to LSA Michigan, “the system is based on several levels of access authorization, where higher levels can open lower levels,” creating a complex but flexible security infrastructure.
Key Hierarchy Mechanism
The fundamental principle of master key systems involves multiple key levels:
Bottom Level: Individual Keys
- Open specific, designated locks
- Restricted to particular rooms or areas
Middle Level: Departmental Master Keys
- Open multiple locks within a specific section
- Provide broader but controlled access
Top Level: General Master Key (GMK)
- LSA Michigan notes this is “the top-level key… [that] can open all doors in the security locking system”
- Highest level of access authorization
- Typically reserved for senior management or facility administrators
The intricate design allows organizations to implement granular access controls while maintaining overall system flexibility. Property managers can strategically distribute key access levels, ensuring that maintenance staff, department heads, and executive leadership have appropriate entry permissions.
Risk Management Considerations
University of Alaska Fairbanks emphasizes that master keys “pose the greatest risk and impact to the key system if lost,” highlighting the critical importance of secure key management protocols. Organizations must implement robust tracking, accountability, and potential re-keying procedures to mitigate potential security vulnerabilities.
By understanding these intricate functional dynamics, organizations can design master key systems that balance accessibility, security, and operational efficiency. Learn more about key management best practices in our comprehensive guide.
Legal and Security Aspects of Usage
Master key systems present complex legal and security considerations that organizations must carefully navigate. University of Alaska Fairbanks warns that master keys “pose the greatest risk and impact to the key system if lost,” underscoring the critical importance of robust security protocols.
Key Legal Considerations
Legal responsibilities associated with master key systems include:
- Duty of Care: Ensuring proper key management
- Liability Protection: Implementing strict access controls
- Confidentiality: Preventing unauthorized key duplication
- Privacy Compliance: Protecting individual access rights
The potential legal risks are substantial. Unauthorized access or key loss can result in significant liability for property owners, potentially exposing them to:
- Security breaches
- Potential property damage
- Personal safety risks
- Potential legal claims
Security Vulnerability Management
LSA Michigan emphasizes that while “master keying provides both security and convenience,” the system’s effectiveness depends entirely on rigorous management protocols. Organizations must implement comprehensive strategies to mitigate risks, including:
- Regular key audits
- Strict key distribution procedures
- Immediate re-keying after key loss
- Comprehensive access tracking
Property managers and business owners must treat master key systems as dynamic security infrastructures requiring constant vigilance. The potential consequences of negligence extend beyond immediate security concerns to potential legal and financial repercussions.
Understanding these nuanced legal and security dimensions is crucial for responsible master key system implementation. Learn more about security best practices in our comprehensive safety guide.
Benefits, Drawbacks, and Common Pitfalls
Master key systems represent a sophisticated yet complex security solution that requires careful consideration. LSA Michigan describes these systems as “an effective and economical way to obtain access control, providing both security and convenience,” while simultaneously acknowledging their potential vulnerabilities.
Key Benefits
Master key systems offer significant advantages for organizations:
- Simplified Access Management
- Reduce total number of physical keys
- Streamline key distribution processes
- Granular Security Control
- Create hierarchical access levels
- Customize permissions for different roles
- Cost-Effective Solution
- Minimize lock replacement expenses
- Centralize key management infrastructure
Critical Drawbacks and Risks
University of Alaska Fairbanks warns that master keys “pose the greatest risk if lost, as they can open all locks in a building.” The potential pitfalls include:
Security Vulnerabilities
- Compromised master keys expose entire systems
- Potential for unauthorized building access
- High-stakes security risks
Complexity in Management
- Requires meticulous tracking protocols
- Demands consistent key audit procedures
- Potential for human error
Common Implementation Mistakes
Organizations frequently encounter challenges when deploying master key systems:
- Inadequate key tracking mechanisms
- Insufficient background checks for key holders
- Delayed re-keying after personnel changes
- Lack of comprehensive access documentation
Understanding these nuanced dynamics helps organizations make informed decisions about implementing master key infrastructures. Proactive management and strategic planning are essential to maximize security benefits while minimizing potential risks. Learn more about key management best practices in our comprehensive security guide.
Secure Your Property with Expert Master Key Solutions
Understanding master key systems is the first step toward smarter access control and enhanced security. If you are managing a building or facility in the GTA and want to protect your property without the hassle of carrying multiple keys, mastering how these systems work can save you time and worry. The challenges of lost master keys, security risks, and complex key hierarchies call for professional locksmith assistance that ensures your system is both secure and manageable.
Don’t let the risks of ineffective key management compromise your safety. Trust My Locksmiths to provide fast, reliable master key system services tailored to your residential or commercial needs. With 24/7 availability across neighborhoods like Etobicoke, Oakville, and Richmond Hill, our licensed technicians handle everything from installation to rekeying with expert care. Learn more about our services in the Uncategorized – My Locksmiths and explore how we transform access control. Ready to upgrade your security? Visit My Locksmiths now and request immediate service to protect what matters most.
Frequently Asked Questions
What is a master key?
A master key is a specialized key that can open multiple locks within a specific system, allowing for controlled access in residential, commercial, and institutional settings.
How do master key systems function?
Master key systems operate through a hierarchical mechanism, where different levels of keys provide varying degrees of access. For example, individual keys open specific locks, while a general master key can unlock all doors in the system.
What are the benefits of using a master key system?
Master key systems simplify access management by reducing the number of physical keys, offering granular security control through hierarchical access levels, and providing a cost-effective solution by minimizing lock replacement expenses.
What are the risks associated with master key systems?
The primary risks include security vulnerabilities if a master key is lost, which can lead to unauthorized access, as well as complexity in management due to the need for meticulous tracking and key audits.






