Access control systems are reshaping how buildings and workplaces stay protected and organized. Forget simple locks and metal keys. Now you have high-tech solutions that use smart cards or even biometrics to let people in or keep them out. This shift is massive and the numbers back it up. Biometric authentication in access control has skyrocketed by 300 percent in the past five years alone. Most people expect fancy tools to add more hassle to daily routines. Instead, these systems actually make security smoother and give organizations major peace of mind you might have never expected.
Table of Contents
- What Are Access Control Systems And Their Purpose?
- The Importance Of Access Control Systems In Security
- How Access Control Systems Work: Technology Behind The Scenes
- Key Components Of Access Control Systems Explained
- Real-World Applications Of Access Control Systems
Quick Summary
| Takeaway | Explanation |
|---|---|
| Access control systems enhance security significantly | These systems regulate access to areas, preventing unauthorized entry and protecting assets effectively. |
| Biometric authentication is increasingly critical | Adoption of biometric methods like fingerprint and facial recognition has ballooned, enhancing security beyond traditional methods. |
| Granular access permissions improve operational efficiency | Customizable permissions allow organizations to manage who can access specific areas based on roles diligently. |
| Real-time monitoring enables rapid threat response | Systems provide immediate alerts on unauthorized access attempts, facilitating quick action to potential security threats. |
| Integration with other technologies enhances protection | Access control systems work alongside other security measures, creating a cohesive and highly secure environment. |
What are Access Control Systems and Their Purpose?
Access control systems represent sophisticated security solutions designed to regulate and monitor entry and exit points in various environments. These intelligent systems go far beyond traditional lock and key mechanisms, providing comprehensive protection and detailed tracking of who enters and leaves a specific space.
Core Definition and Fundamental Purpose
At its most basic level, an access control system is a technology-driven mechanism that manages and restricts physical entry to buildings, rooms, or designated areas. Unlike conventional locks, these systems use advanced authentication methods to verify an individual’s authorization before granting entry. Learn more about modern security technologies that are transforming how we protect our spaces.
The primary purpose of access control systems includes:
- Preventing unauthorized entry and protecting valuable assets
- Creating detailed logs of all entrance and exit events
- Enabling precise control over who can access specific areas
- Reducing the risk of potential security breaches
Authentication and Verification Methods
Modern access control systems employ multiple verification techniques to ensure robust security. These methods can range from traditional methods like physical key cards to more advanced biometric technologies such as fingerprint scanners, facial recognition, and retinal authentication. According to Cybersecurity Ventures, biometric authentication methods have seen a 300% increase in adoption across commercial and residential settings in the past five years.
The authentication process typically involves three critical components: identification, authentication, and authorization. An individual must first identify themselves, then prove their identity through a credential or biometric scan, and finally receive authorization based on their predetermined access rights. This multilayered approach ensures that only verified individuals can enter secured spaces, dramatically reducing potential security risks.
Below is a table summarizing the main authentication and verification methods used in access control systems and their key characteristics.
| Authentication Method | Description | Key Benefit |
|---|---|---|
| Key Card | Physical card with encoded data | Easy to use and distribute |
| Biometric (Fingerprint) | Scans unique fingerprint patterns | High accuracy and security |
| Facial Recognition | Identifies users by facial features | Hands-free convenience |
| Retinal Authentication | Scans the unique pattern of the retina | Extremely difficult to forge |
| PIN/Password | User enters a personal identification number or password | Simple implementation |
| Mobile Credential | Uses a smartphone app or Bluetooth feature | Convenient and remote control |
By implementing sophisticated access control systems, organizations and property owners can create granular, intelligent security environments that adapt to changing security requirements while providing comprehensive monitoring and protection.
The Importance of Access Control Systems in Security
Access control systems have become critical components in modern security infrastructure, offering far more comprehensive protection than traditional security measures. These advanced technological solutions provide organizations and property owners with sophisticated mechanisms to safeguard physical and digital assets against potential security threats.
Protecting Against Unauthorized Access
The fundamental role of access control systems is preventing unauthorized entry into secured spaces. By establishing strict verification protocols, these systems create multiple layers of security that significantly reduce the risk of potential breaches. Explore advanced commercial security solutions that can transform your protection strategy.
Key benefits of robust access control include:
- Immediate identification and tracking of all individuals entering a space
- Real-time alerts for suspicious or unauthorized access attempts
- Comprehensive documentation of entry and exit events
- Flexible permission management for different user groups
Mitigating Security Risks and Potential Threats
Modern security challenges require dynamic and intelligent solutions. Access control systems go beyond simple entry restrictions by providing advanced threat detection and prevention capabilities. According to Gartner Security Research, organizations implementing comprehensive access control strategies experience up to 67% reduction in security incidents.
These systems enable precise monitoring and management of who can access specific areas, creating an intelligent security ecosystem that adapts to changing organizational needs. By implementing granular access permissions, businesses can protect sensitive areas, restrict unauthorized personnel from critical infrastructure, and maintain a clear audit trail of all movements.
Moreover, access control systems integrate seamlessly with other security technologies, creating a holistic approach to protection. The ability to remotely manage access rights, instantly revoke credentials, and generate detailed activity reports makes these systems invaluable tools in contemporary security management.
By investing in sophisticated access control technologies, organizations can create secure, intelligent environments that protect people, assets, and information with unprecedented precision and effectiveness.
How Access Control Systems Work: Technology Behind the Scenes
Access control systems represent complex technological ecosystems that combine hardware, software, and sophisticated authentication protocols to create intelligent security environments. These systems function through intricate networks of interconnected components designed to verify, authorize, and monitor individual access across various physical and digital spaces.
Core Authentication Components
The technological infrastructure of access control systems relies on three primary elements: credentials, readers, and control panels. Discover more about keyless security innovations that are revolutionizing how we protect spaces. Each component plays a critical role in the authentication process:
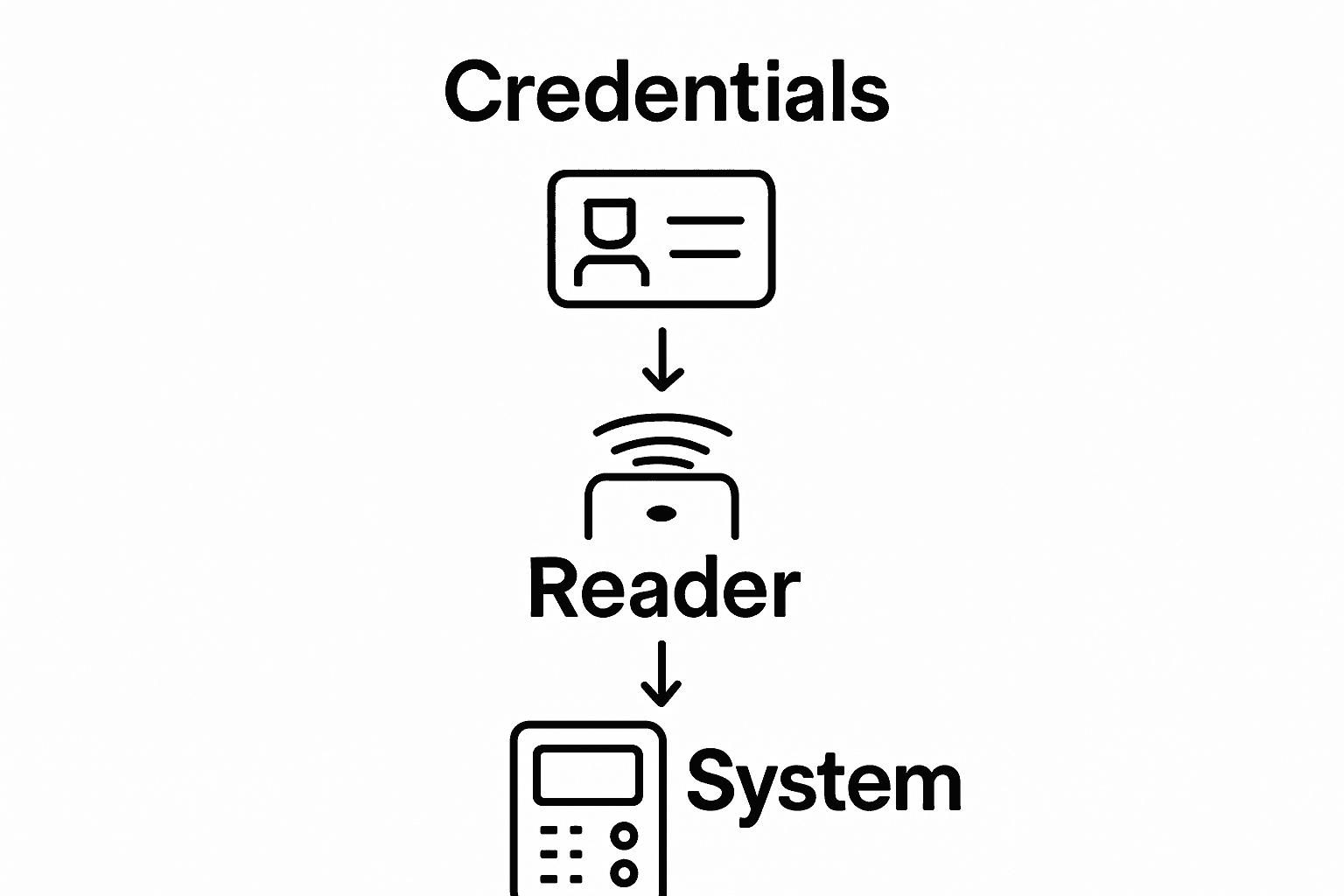
- Credentials: Physical or digital tokens that identify authorized individuals
- Readers: Devices that capture and process credential information
- Control Panels: Central processing units that make authorization decisions
Authentication Workflow and Decision Making
The authentication process follows a precise sequence of technological interactions. According to National Institute of Standards and Technology, access control mechanisms evaluate multiple parameters to determine entry permissions.
When an individual presents their credential, the system initiates a complex verification process. The reader captures the credential’s unique identifier, transmits this information to the control panel, which cross-references the data against predefined access rules. This multilayered verification ensures that only authenticated and authorized individuals can enter secured areas.
Modern access control systems incorporate advanced technologies such as biometric scanning, cryptographic authentication, and machine learning algorithms. These technologies enable dynamic risk assessment, allowing systems to adapt and respond to potential security threats in real time. By analyzing patterns of movement, detecting anomalies, and maintaining comprehensive logs, these intelligent systems provide unprecedented levels of security monitoring and protection.
The technological sophistication of access control systems transforms traditional security approaches, creating adaptive, intelligent environments that can protect people, assets, and information with remarkable precision and efficiency.
Key Components of Access Control Systems Explained
Access control systems are intricate networks of technological components working seamlessly to provide comprehensive security solutions. Understanding these individual elements is crucial for appreciating how modern security infrastructures protect physical and digital spaces from unauthorized access.
Hardware Elements and Authentication Devices
The physical foundation of access control systems comprises multiple sophisticated hardware components. Learn more about advanced key management strategies that complement these technological solutions. These essential hardware elements include:
- Access Cards/Credentials: Physical or digital tokens with unique identifiers
- Card Readers: Devices that scan and interpret credential information
- Electronic Locks: Mechanisms triggered by successful authentication
- Biometric Scanners: Advanced devices capturing unique physical characteristics
Software and Intelligent Management Platforms
Behind the hardware infrastructure, powerful software platforms manage and coordinate access control operations. According to Security Industry Association, modern access control software provides comprehensive management capabilities that extend far beyond simple entry restriction.
These intelligent platforms enable administrators to:
- Configure granular access permissions
- Monitor real-time entry and exit logs
- Generate detailed security reports
- Remotely manage and update access credentials
- Integrate with broader security ecosystem technologies
The software component acts as the central nervous system, processing authentication requests, comparing credentials against predefined rules, and making split-second decisions about granting or denying access. Advanced machine learning algorithms enhance these platforms, enabling predictive threat detection and adaptive security responses.
By combining robust hardware infrastructure with intelligent software management, access control systems create dynamic, responsive security environments that can protect complex organizational spaces with unprecedented precision and efficiency.
The following table outlines core hardware and software components found in modern access control systems, along with a short explanation of each element.
| Component Type | Example Devices/Platforms | Functionality Description |
|---|---|---|
| Credential | Access cards, mobile apps | Identify authorized users |
| Reader | Card readers, biometric devices | Capture and transmit credential information |
| Electronic Lock | Electric strikes, maglocks | Secure physical entry points; unlock with valid authentication |
| Control Panel | Central controller unit | Processes requests and grants or denies access |
| Management Software | Access control software | Manages permissions, logs events, and enables remote control |
| Biometric Scanner | Fingerprint, facial devices | Verifies unique physical characteristics |

Real-World Applications of Access Control Systems
Access control systems have transformed security strategies across diverse industries, offering sophisticated solutions that extend far beyond traditional lock and key mechanisms. These technological innovations provide organizations with powerful tools to manage and protect their most critical assets, people, and information.
Protecting Critical Infrastructure and Sensitive Environments
Certain sectors demand exceptionally rigorous security protocols where access control systems play a pivotal role. Learn more about specialized security solutions that can safeguard complex environments. Critical sectors utilizing these systems include:
- Healthcare Facilities: Protecting patient records and restricted medical zones
- Government Buildings: Securing sensitive administrative and research spaces
- Financial Institutions: Restricting access to vault areas and confidential data centers
- Research Laboratories: Controlling entry to specialized scientific research environments
Industry-Specific Security Applications
Access control systems offer tailored security approaches that adapt to unique organizational requirements. According to National Institutes of Health, healthcare institutions demonstrate how granular access management can significantly enhance operational security and patient privacy.
In corporate environments, these systems enable sophisticated permission management. Employees can be granted precisely defined access levels based on their roles, departments, and specific organizational responsibilities. This approach minimizes potential internal security risks while maintaining operational efficiency.
Manufacturing facilities utilize access control systems to protect intellectual property, regulate equipment usage, and maintain strict safety protocols. By implementing multilayered authentication processes, these systems prevent unauthorized personnel from entering high-risk production areas, thereby reducing potential workplace accidents and industrial espionage risks.
The versatility of modern access control technologies allows organizations to create intelligent, adaptive security ecosystems that respond dynamically to evolving threat landscapes while maintaining streamlined operational workflows.
Take Control of Your Security with Trusted Local Experts
Worried about unauthorized access or not sure if your property is truly secure? As this article highlights, modern access control systems provide a smarter way to protect what matters most. You need solutions that do more than just lock the door. You deserve professional service, rapid response, and complete peace of mind.
My Locksmiths specializes in access control systems and security upgrades throughout the Greater Toronto Area. Whether you want to enhance entry monitoring, manage permissions across your business, or secure your home with smart technology, our licensed technicians are on call day and night. See how easy it is to upgrade your protection and experience service backed by a proven record of reliability and customer satisfaction. Visit My Locksmiths now or contact us today for fast security help.
Frequently Asked Questions
What are access control systems?
Access control systems are security solutions designed to manage and restrict physical entry to buildings or areas using advanced authentication methods instead of traditional locks.
How do access control systems enhance security?
They enhance security by preventing unauthorized entry, creating detailed logs of access events, and providing real-time alerts for suspicious activities, thereby significantly reducing security risks.
What types of authentication methods are used in access control systems?
Access control systems use various authentication methods, including physical key cards, biometric scans (like fingerprints and facial recognition), and cryptographic authentication for secure verification.
What are the advantages of implementing access control systems in an organization?
Implementing access control systems offers multiple advantages, including enhanced protection of sensitive areas, improved tracking of individuals entering and exiting facilities, and the capability to manage permissions based on user roles within the organization.







