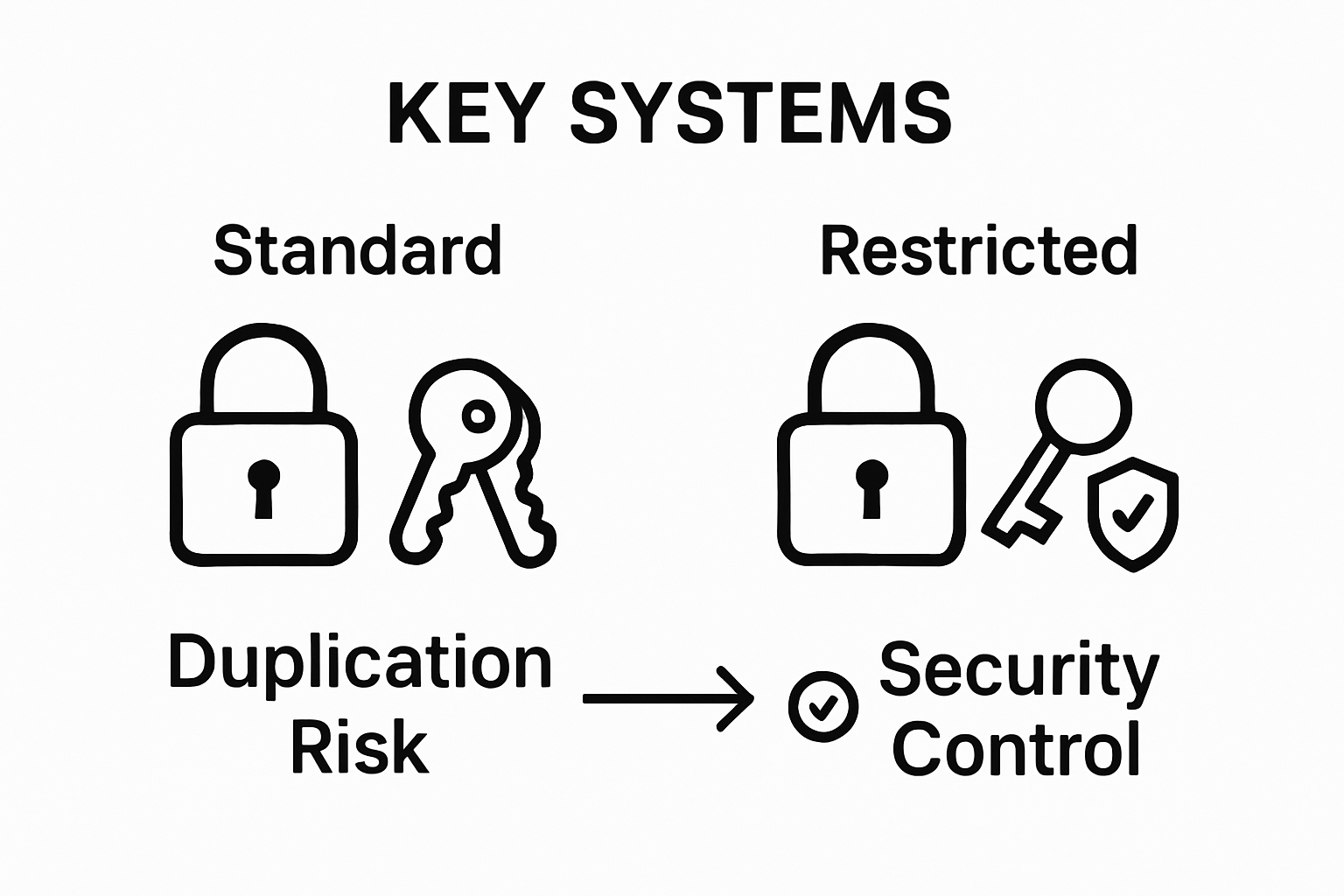
Restricted key systems might sound like a simple tweak to regular locks, but they quietly safeguard some of the most sensitive facilities in the world. Nearly 90 percent of major institutions now choose restricted systems over traditional locks, mainly to stop unauthorized key duplication. You might expect the magic lies in high-tech electronics, yet the real power comes from patent-protected keys and tight control over who gets copies. There is more to this security upgrade than meets the eye.
To help clarify the major differences between traditional locks and restricted key systems, the following table compares their features and security advantages.
| Feature/Characteristic | Traditional Lock System | Restricted Key System |
|---|---|---|
| Key Duplication Control | Can be copied anywhere | Only authorized dealers/manufacturers can duplicate |
| Keyway Design | Standard, widely available | Proprietary, legally protected |
| Security Level | Moderate | High |
| Access Tracking | Not usually tracked | Comprehensive tracking and registration |
| Legal Protections Against Duplication | Minimal or none | Strong patent and legal restrictions |
| Hierarchical Access Capability | Limited or manual | Granular, easy to program |
| Best Suited For | Low to moderate security needs | High-security, institutional, or sensitive environments |
Table of Contents
- What Are Restricted Key Systems And Their Purpose?
- The Importance Of Restricted Key Systems In Security
- How Restricted Key Systems Function And Key Concepts
- Real-World Applications Of Restricted Key Systems
Quick Summary
| Takeaway | Explanation |
|---|---|
| Restricted key systems enhance security | These systems prevent unauthorized key duplication, significantly improving security in various environments. |
| Unique key designs deter theft | Proprietary designs make unauthorized copying nearly impossible, safeguarding sensitive areas efficiently. |
| Granular access control is achievable | Organizations can create Hierarchical access levels for employees, enhancing security accountability. |
| Comprehensive tracking of key distribution | Detailed records of who has keys and when enhances oversight, minimizing security risks. |
| Applicable to diverse sectors | Used in government, corporate, and educational settings, these systems adapt to various security needs effectively. |
What Are Restricted Key Systems and Their Purpose?
Restricted key systems represent a sophisticated security solution designed to provide controlled and precise access management for various environments. At their core, these systems limit key duplication and unauthorized access through specialized design and legal protections.
The Fundamental Concept of Key Restriction
A restricted key system fundamentally differs from traditional lock and key arrangements. In these systems, key blanks and keyway designs are exclusively controlled by specific manufacturers, making unauthorized key reproduction nearly impossible.
 The master key systems guide provides deeper insights into advanced access control strategies.
The master key systems guide provides deeper insights into advanced access control strategies.
Under this approach, each key is uniquely registered and tracked. According to the U.S. Forest Service security guidelines, restricted keyways prevent easy duplication by implementing several critical safeguards:
- Proprietary key blank designs that cannot be purchased publicly
- Legal restrictions preventing unauthorized key reproduction
- Specialized manufacturing processes that limit key template access
Strategic Security Advantages
Restricted key systems offer multiple security benefits beyond standard lock mechanisms. Organizations and property managers gain enhanced control by:
- Preventing unauthorized personnel from creating duplicate keys
- Maintaining precise accountability for key distribution
- Creating hierarchical access levels within complex environments
These systems are particularly valuable in high-security settings such as government facilities, corporate offices, educational institutions, and sensitive research environments where controlled access is paramount.
By eliminating the risk of casual key copying, restricted key systems provide a robust layer of security that traditional locks cannot match.
The Importance of Restricted Key Systems in Security
Restricted key systems represent more than just a technical security solution they are a strategic approach to protecting physical spaces and sensitive assets. By implementing these advanced access control mechanisms, organizations can significantly mitigate unauthorized entry risks and maintain comprehensive security protocols.
Preventing Unauthorized Key Duplication
The primary security advantage of restricted key systems lies in their ability to prevent unauthorized key reproduction. Commercial door lock types vary widely, but restricted systems offer unparalleled protection. According to the U.S. Forest Service security guidelines, these systems implement critical safeguards that traditional locks cannot match:
- Unique keyway designs that cannot be easily replicated
- Legal protections against unauthorized key blank manufacturing
- Strict control over key distribution and tracking
Comprehensive Access Management
Restricted key systems provide organizations with granular control over physical access. Security managers can create complex hierarchical access levels, ensuring that employees only enter areas relevant to their roles. This approach minimizes potential security breaches by:

- Establishing clear access boundaries
- Creating traceable key distribution records
- Limiting potential insider security risks
By integrating restricted key systems, businesses transform their security from reactive to proactive. These systems do not just prevent unauthorized entry they create an intelligent, manageable access environment that adapts to organizational needs while maintaining robust security protocols.
The table below summarizes the key strategic advantages of restricted key systems, as discussed in the article.
| Strategic Advantage | Explanation |
|---|---|
| Prevents Unauthorized Key Duplication | Proprietary keys and legal controls stop copying by outsiders |
| Enables Hierarchical Access Control | Supports varying levels of access for different personnel |
| Offers Detailed Key Distribution Tracking | Maintains records for who has each key and when issued |
| Enhances Physical Security | Reduces risks of theft, intrusion, and internal misuse |
| Adapts to Many Sectors | Suitable for government, business, education, and infrastructure |
How Restricted Key Systems Function and Key Concepts
Restricted key systems operate through a complex mechanism of technological and legal controls that transform traditional lock and key infrastructure into a highly secure access management solution. These sophisticated systems go far beyond conventional security approaches by integrating advanced design principles and strict regulatory frameworks.
Technical Design and Architectural Complexity
At the heart of restricted key systems lies a unique architectural design that prevents unauthorized key reproduction. Keyless entry systems offer alternative security strategies, but restricted key systems provide a mechanical approach with multilayered protection. According to the U.S. Forest Service security guidelines, these systems implement several critical technical components:
- Proprietary keyway geometries with intricate cutting patterns
- Specialized key blank designs that cannot be commercially purchased
- Registered and serialized key identification mechanisms
Authorization and Control Mechanisms
The function of restricted key systems extends beyond physical design into a comprehensive authorization framework. Organizations can establish precise access hierarchies by:
- Creating multiple levels of key authorization
- Implementing strict key distribution protocols
- Maintaining detailed records of key issuance and usage
These systems transform key management from a simple mechanical process into a strategic security protocol. By combining technological innovation with rigorous administrative controls, restricted key systems provide an intelligent solution that adapts to complex organizational security requirements while maintaining unparalleled access management precision.
Real-World Applications of Restricted Key Systems
Restricted key systems are not merely theoretical security concepts but practical solutions deployed across diverse sectors to protect critical assets, sensitive spaces, and organizational infrastructure. These advanced access control mechanisms offer tailored security strategies that adapt to unique institutional requirements.
Critical Infrastructure and Government Facilities
Government and high-security environments represent the most sophisticated implementation of restricted key systems. Top commercial door lock types demonstrate the complexity of security needs, but restricted key systems provide unparalleled protection. According to the U.S. Forest Service security guidelines, these systems are crucial in protecting sensitive areas by:
- Securing classified research facilities
- Controlling access to critical infrastructure zones
- Protecting high-risk governmental installations
Corporate and Educational Institutional Security
Business and academic environments leverage restricted key systems to manage complex access requirements. Organizations implement these systems to address multifaceted security challenges such as:
- Establishing hierarchical access levels for different employee roles
- Protecting intellectual property and research materials
- Managing multi-building campus security infrastructures
By integrating restricted key systems, institutions create dynamic security ecosystems that respond intelligently to organizational complexity. These systems transform traditional lock and key approaches into strategic access management tools that provide granular control, comprehensive tracking, and robust protection against unauthorized entry.
Secure Your Property with Professional Restricted Key Solutions
Is worrying about unauthorized key duplication or gaps in your property’s security keeping you up at night? As discussed in “Understanding Restricted Key Systems for Better Security,” not having a reliable restricted key system leaves your home or business vulnerable to key copying and unauthorized entry. You deserve precise access control, legal protection against duplication, and peace of mind knowing only trustworthy hands hold your keys. At My Locksmiths, we specialize in the installation and management of advanced key control systems tailored to your needs, so you never have to second-guess your building’s safety.
Take action now and eliminate guesswork from your security strategy. Our expert technicians are ready 24/7 across the Greater Toronto Area and are equipped to upgrade your property with proven access management tools. Ready to make your security proactive instead of reactive? Connect with the leading locksmith professionals in Toronto for a custom consultation and immediate service. Get protected today—your keys and your peace of mind are just a click away.
Frequently Asked Questions
What is a restricted key system?
A restricted key system is a sophisticated security solution that limits key duplication and unauthorized access through proprietary key designs and legal protections.
How do restricted key systems prevent unauthorized key duplication?
These systems use unique keyway designs and proprietary key blanks that are not available for public purchase, along with strict legal restrictions on key reproduction.
What are the strategic advantages of using restricted key systems?
Restricted key systems provide enhanced control over who can access specific areas, prevent unauthorized key duplication, and allow organizations to create hierarchical access levels for employees based on their roles.
Where are restricted key systems commonly used?
They are typically implemented in high-security environments such as government facilities, corporate offices, educational institutions, and sensitive research facilities to manage access and protect critical assets.







